One character. That’s the gap.
What a Friday afternoon wire transfer taught me about data protection.
Last week I wrote about text messages. The spam that looks even better than the real thing. Same timing. Right carrier, right moment, right enough to fool you.
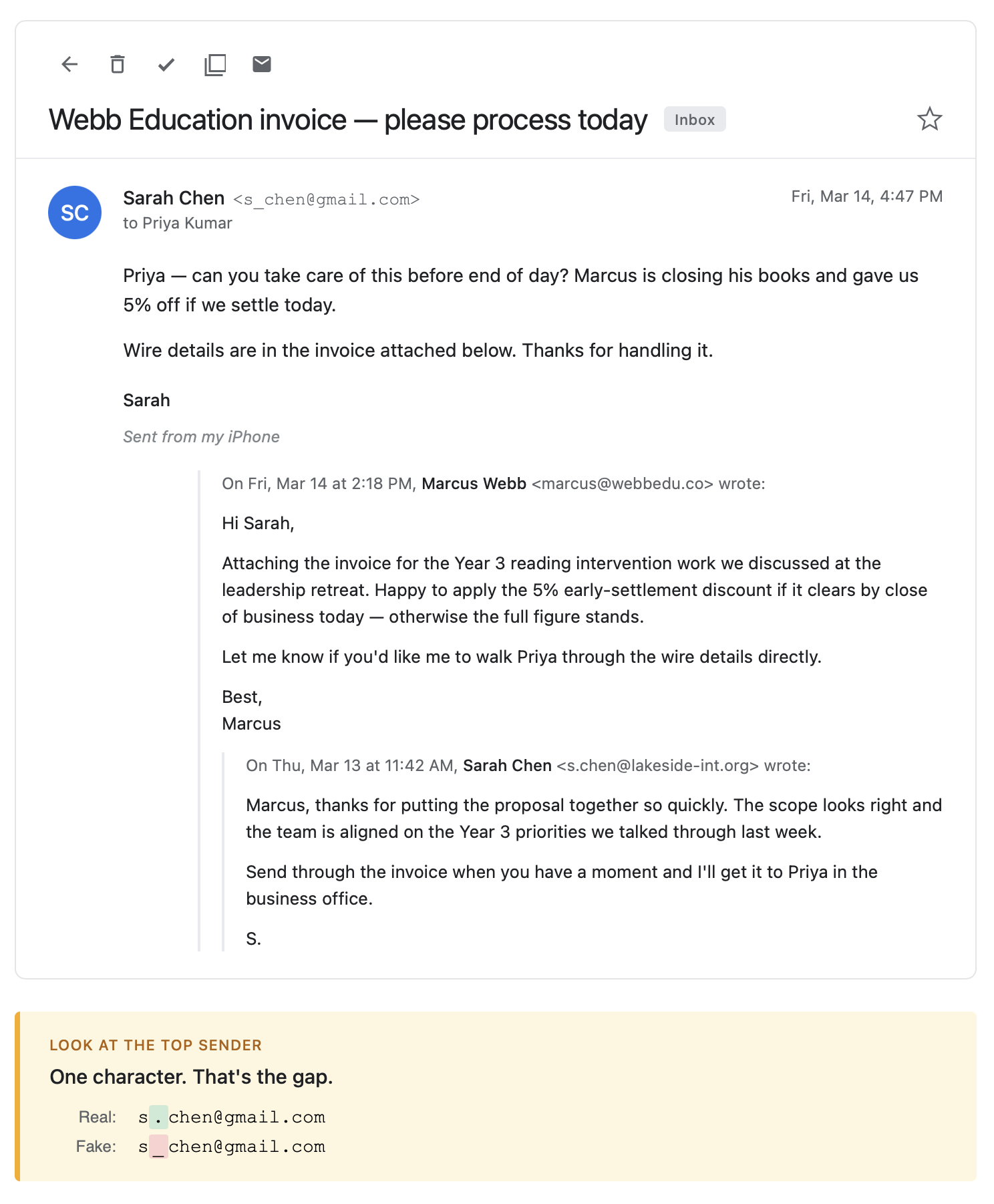
The same thing is happening in your inbox. And it's more sophisticated.
A phishing email from what looks like a trusted colleague. The right name. A real project. Sent on a Friday afternoon when people are moving fast. These aren't lucky guesses. They're built from data. And most of that data wasn't stolen from anywhere.
A few years ago, a school I worked at got hit by a Business Email Compromise attack. A colleague who handled outgoing payments received an email on a Friday afternoon. The subject line said urgent. The sender appeared to be a senior leader at the school.
The address looked right at a glance. It was coming from something that resembled the leader's personal Gmail rather than a school account. That detail almost got lost. It was Friday. There was an entire thread sitting above the request.
The thread was the thing.
It wasn't just an email asking for a wire transfer. It was a conversation. Casual. Unhurried. The kind of back-and-forth that happens between two people who have worked together before. A senior leader and a consultant discussing a project tied to something we were actually working on. An original invoice. A request for a discount if payment cleared before the weekend. The tone of the exchange, the dates of the emails – all of it looked right.
Buried at the bottom was a forwarded note. Something like: can you please take care of this before the end of the day? The amount wasn't enormous. The project mapped onto something real. The consultant had a website and a LinkedIn profile. Both had been built well enough to survive a quick look.
Here is what the attackers needed to pull that off.
They needed to know the leader's personal email address, or something close to it. Not the school account, which is public, but something that looked like a personal account rather than a work one. They needed to know enough about our priorities to name a plausible project. They needed a sense of how that person wrote in low-stakes messages. And they needed to know which colleague handled outgoing payments.
Here is the part worth sitting with. None of that information is secret. None of it came from a breach. It was assembled.
School websites publish their priorities. LinkedIn connects staff to roles, institutions, and the conferences they've presented at. Conference programs name presenters and their schools. A personal email address can often be constructed from naming patterns you can find across public sources. Or purchased outright from data brokers. A senior leader's writing style is in every staff newsletter, every public presentation, every communication they've ever sent.
The attackers didn't need one sensitive file. They needed enough small, harmless, public pieces to build something that looked real from the inside.
The fake address had the same first and last name as the real one, with an underscore where the real address used a period.
One character. That's the gap.
There’s a name for what the attackers did. Intelligence analysts call it the mosaic effect. The idea is that individually harmless pieces of information, combined, reveal something that none of them could reveal alone. A name. A role. A school priority. A writing style. A personal email pattern. Who handles payments. Each tile is unremarkable. The picture they make together is a working impersonation.
It didn't start in cybersecurity. Analysts in national security came up with it. The problem was that individually unclassified facts, assembled, could reveal something classified. Each piece looked safe to share. The combination didn't.
Here is how we caught it.
The leader happened to walk past the colleague's desk that afternoon. The colleague looked up and mentioned it casually. Just so you know, we're all set to pay the consultant. The leader stopped. No idea what that was about.
That's it. A passing conversation. Nothing systematic. Nothing designed. A different route back to the office and the transfer goes through.
The email sounded exactly like the leader. The project sounded exactly like something we'd commission. The conversation thread sounded exactly like how those negotiations go. None of it raised a flag until the person being impersonated happened to walk by.
The case for protecting data isn't that a breach will happen. It's that the data you hold, share, or leave in circulation is the raw material for attacks you haven't seen yet. The question worth asking, before any of that, is whether you're putting more into circulation than you need to.
Not because something has gone wrong yet. Because combination is the threat. And you're generating the raw material right now.
The details in the story below have been changed to protect the people involved. The attack is real.